A good turn out for a chat that continued till closing time, while near by a small group took CW practice, showing good progress.
Category Archives: Uncategorized
29 May 2025 – An Introduction to ADTV by Matt, G4IYT
Matt began by looking as some of the older Amateur TV formats and frequencies, including analog and digital. He pointed out that analogue was easy to start out with, but the quality was often not up to standard. He said that all amateur bands above 432MHz were available for ATV including 70cm, 13cm, 3.4GHz and 10GHz. Experimental NoVs are available for 71MHz and 146MHz.
He pointed out that analog was widespread till 2015, mostly on 70cms, 8MHz AM, 23cms 16MHz FM, and 13cms 16MHz FM. Some FPV drone gear is still using analog on 5.6GHz because it’s easy to start with but limited and now there are fewer analog repeaters.

Digital is now predominant using DVB-S/DVB-S2 standards, originally for satellite TV. Various modulation modes i.e. QPSK, 8PSK, 16APSK, and 32APPSK. The Coding/FEC options are 1/3 up to 9/10. MPEG transport streams, modern compression. H264, H265, hardware and software encoding and symbol rates 66ks/s to 4Ms/s
Modulation represents digital data as symbols. Such as: Symbol rate = base data rate + FEC. TX Data rate = bits x symbol rate. Higher symbol rate means faster transfer but wider bandwidth. 333Ks/s to 1Ms/s common in DATV.
As for operation, there is Simplex for contesting, /p. and Repeaters such as GB3TV at Dunstable Downs on 23cm and GB3TZ at Caddington on 13cm, plus there are 30 plus more around the UK. Satellite can also be used on QO-100 Wideband (Geo stationary)
Looking back in time, some might remember the lift in the 70s and 80s where 44-55MHz analog signals could be seen worldwide. Rob M0DTS used 100W on 29.250MHz with a 3 element yagi and worked a 5,500km path!
 Matt went on to describe a “basic” set up and other more specialised equipment.
Matt went on to describe a “basic” set up and other more specialised equipment.
He pointed out a good source of information,,The British Amateur Television Club and AMSAT-UK. A Q&A session followed with lots of questions and answers.
my thanks to Matt for providing the necessary data to write this piece.
15 May 2025 – Sporadic-E: A new season upon us – Jim Bacon, G3YLA
We were treated to a fascinating evening by Jim Bacon – G3YLA, who is world renowned for his research into Sporadic-E propagation, which can produce exciting long distance openings on the upper HF and VHF bands.
As we are just entering this year’s sporadic E season, his talk came at the perfect time to help us understand how best to experience this fleeting but effective mode of propagation.

Jim expained that Sporadic-E is a complex yet rewarding subject, influenced by many forces of nature.
It still holds many mysteries, making it a rewarding subject for those with an enquiring mind.
Jim narrowed down the main factors which produce sporadic-E openings to:-
- Meteorite trails, the ‘seeds’ of Es, containing long-living metallic ions, capable of reflecting radio waves.
- Jet streams, whose complex interactions and vortices can concentrate the density of the meteorite’s metallic ion remnants, further enhancing their ability to reflect radio signals.
- Atmospheric Gravity Waves, providing further energy input to compress and move the layer of particles to altitudes which can further enhance the propagation benefits of the Es layer.
Other influences include storms, weather fronts, ridges and the KP index. A high Kp index is harmful to the formation of sporadic E conditions, due to its disruptive energy. Ideally, we need calm solar conditions to allow the Sporadic E active layer to form.

Jim recommends you keep an eye on propquest.co.uk which he has developed and fine tuned over many years to become a uniquely useful tool for everyone interested in propagation
His ‘Es Probability Index’ (EPI) will give you a good feel for the likelihood of Es conditions being available in the short term.
Also look for ridges, storms and a high FoEs value.
We can expect the useful frequency to be around 8-10 times the reported FoEs value.
Openings tend to occur twice daily. Early, just after dawn, when most meteor activity occurs and later in the afternoon, due to diurnal atmospheric tides.
Keep your receiver tuned to 50.095Mhz during May to August and you will almost certainly be rewarded, with patience, with a Sporadic E opening – this could be the start of a whole new fascinating aspect to your hobby!
Good luck! And thank you Jim, for a really fascinating talk!
8 May 2025 – Video evening by Don, G4LOO
This evening the assembled members chose the RSGB 2024 Convention video by Don Beatie, G3BJ titled ‘Spanning the Globe, the dawn of global radio communications’
Don began by saying this isn’t a long time ago, you know. He said he had been licensed 60 years so not very short of the one hundred years we now celebrate as the first radio contact between New Zealand and the UK.
It all came about when Cecil Goyder, (G)2HM an under graduate at what is now the Imperial College London and Frank Bell, a sheep farmer in South Island NZ made a two way radio contact one hundred years ago in October 1924. The frequency was 3.2MHz! Of course all transmissions were made at such a low frequency back then.
Putting all in context, Don said ‘Marconi’s Atlantic leap’ had only happened 24 years before. That was spark transmission and a coherer progressing to valves. Wireless Experimenters numbers were growing and problems due to increasing interference due to the spark transmissions, the Post Office imposed restrictions. Through all this came the ‘Great Leap from UK to NZ’
Don took up 11 key points between 1898 and 1927 which saw progress in radio design and operations.
The entire story can be seen on You Tube by looking up 2024 RSGB.org/conference, and find the title ‘Spanning the Globe, the dawn of global radio communications’ by Don Beatie, G3BJ / G5W
1 May 2025 – Club natter night and Morse Practice evening
A group gathered to hone their Morse code receiving skills with Richard G3NII and Ken G4YRF operating the keys.
We also had a demo from Victor G3JNB, allowing us to hear his amazing little all-band all-mode receiver in action. We strung up a simple wire antenna and signals from all over Europe were heard coming in loud and clear on 20m CW and 40m CW. The receiver also performed impressively on Band II, the FM broadcast band, with Classic FM crisp and clear.

We later had a small huddle, discussing plans for our forthcoming outdoor demo station at the Shefford Summer Fete, on 1st June 2025.
Ken then showed us a fine AI-generated poster on the notice board, which he and his son had prepared, to publicise our club to other users of the hall.
30 April 2025 – Visit to Marshall Amplification plc factory
Wednesday’s Club Visit to Marshalls was a great success.
Steve Hill our guide was very knowledgeable and we started off with a visit to the museum collection of amplifiers and speakers along with some of the guitars used, many owned by pop stars though time.

We saw the very first amplifier made by Marshalls and had explained to us the history of the company, which was formed back in the 1960’s
Originally formed in London by Jim and Terry Marshall, the company moved to Bletchley, where they are today. The products are hand made with circuit boards wired and soldered individually before being install into their chassis.
We were shown round the production line where each part was built and eventually constructed into the specific product. In a separate part of the factory we watched the wooden cabinets being constructed and finished through a heating process before being painted.

All in all the guided tour was most interesting. Our guide made the tour, giving us all the little interesting facts about the products and the stars that used them.
Marshalls would welcome us back at some time in the future, which will be an opportunity for those who did not make it this to enjoy a bit of British pop history.
Visit their website at:
https://www.marshall.com/gb/en/about-marshall
24 April 2025 – 100 years of radio by Paul G8IUG
It all started with Heinrich Hertz a physicist born in Germany in 1857 who first conclusively proved the existence of the electromagnetic waves predicted by James Clerk Maxwell’s equations of electromagnetism.
With the onset of radio use it was thought to be prudent to be able to monitor radio waves and that saw the beginning of GCHQ before WW l
During WW I spark transmitters were replaced by those using valves.
Bletchley Park was set up as a very secret unit near the start of WW ll .Transistors also came into use at about this time. Eddystone radio became Marconi and radios moved to include not just LF and HF but frequencies in the Gigahertz range for use with RADAR.
The famous 19 set was included in all tanks during WW ll.
As well as transistors the new Integrated circuits came into use
Paul had many projects to display and books to recommend.
10 April 2025 – Spring surplus equipment sale
A good turnout, including two visitors, saw Don, G4LOO and David, G8UOD at work as the ‘Auctioneers.
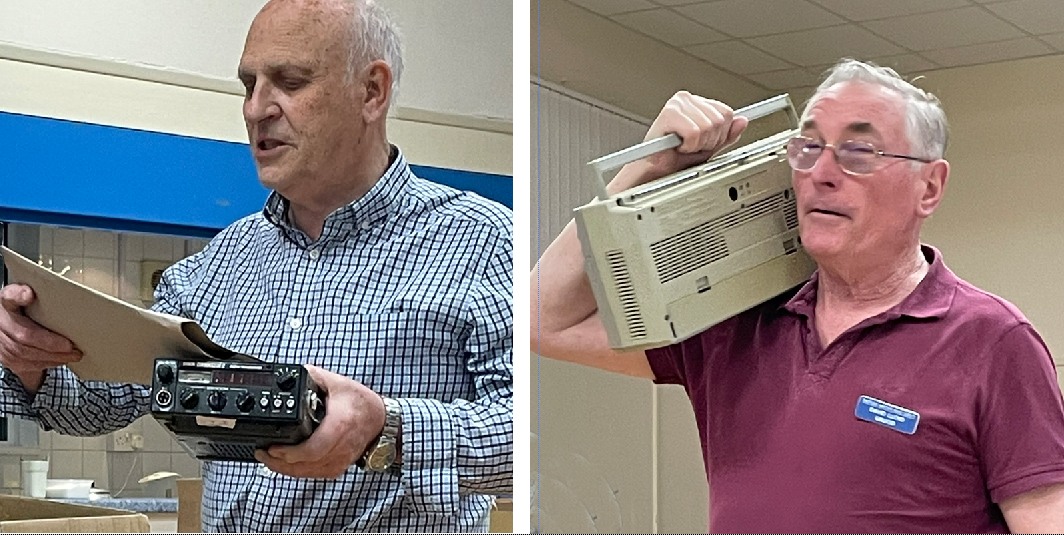


And lots more!
3 April 2025 – Royal Observer Corps history – Above & Below Ground by John Shere.
After his time in the RAF, John said in 1980 he joined the Royal Observer Corps.

Speaking of the history, he said during 1925 as part of preparations for war the Observer Corps was formed as part of the UK’s aerial defence. The purpose was to report and track enemy and allied aircraft across London and areas South. It became part of the Air Ministry in 1929. By the start of WWll The Observer Corps Air Defence System had covered the entire country. The organisation was granted Royal status in 1941 in recognition of their service during the Battle of Britain.
Also in 1941 women were accepted for the first time. Later in 1944, volunteers rose to 1000 and were tasked with the identification of allied and enemy aircraft During the D-Day Landings. In 1945 the Corps were stood down, but during 1947 the Corps were remobilized to face the Cold War threat. They would monitor and warn of a nuclear attack and track radio active fallout if detected. To facilitate this almost 1500 underground posts were created. The Corps undertook regular drills and training till 1980s when reduced tensions between East and West reduced the need for warnings and monitoring.
In 1995 The Corps was finally stood down.

The Blast Recorder
27 March 2025 – Natter and CW practice
A good turnout for this evening’s CW practice with Richard G3NII at the key. All members are welcome even if you want to learn, just come along on the evenings listed on our programme.